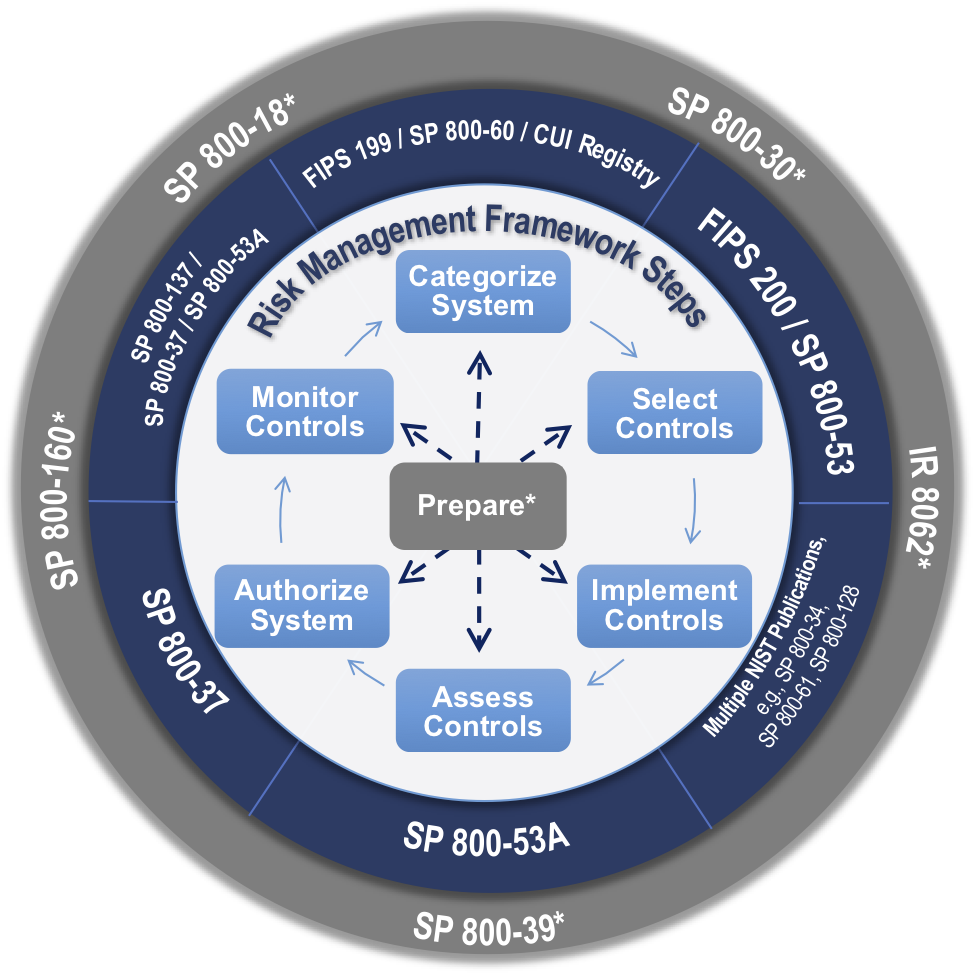
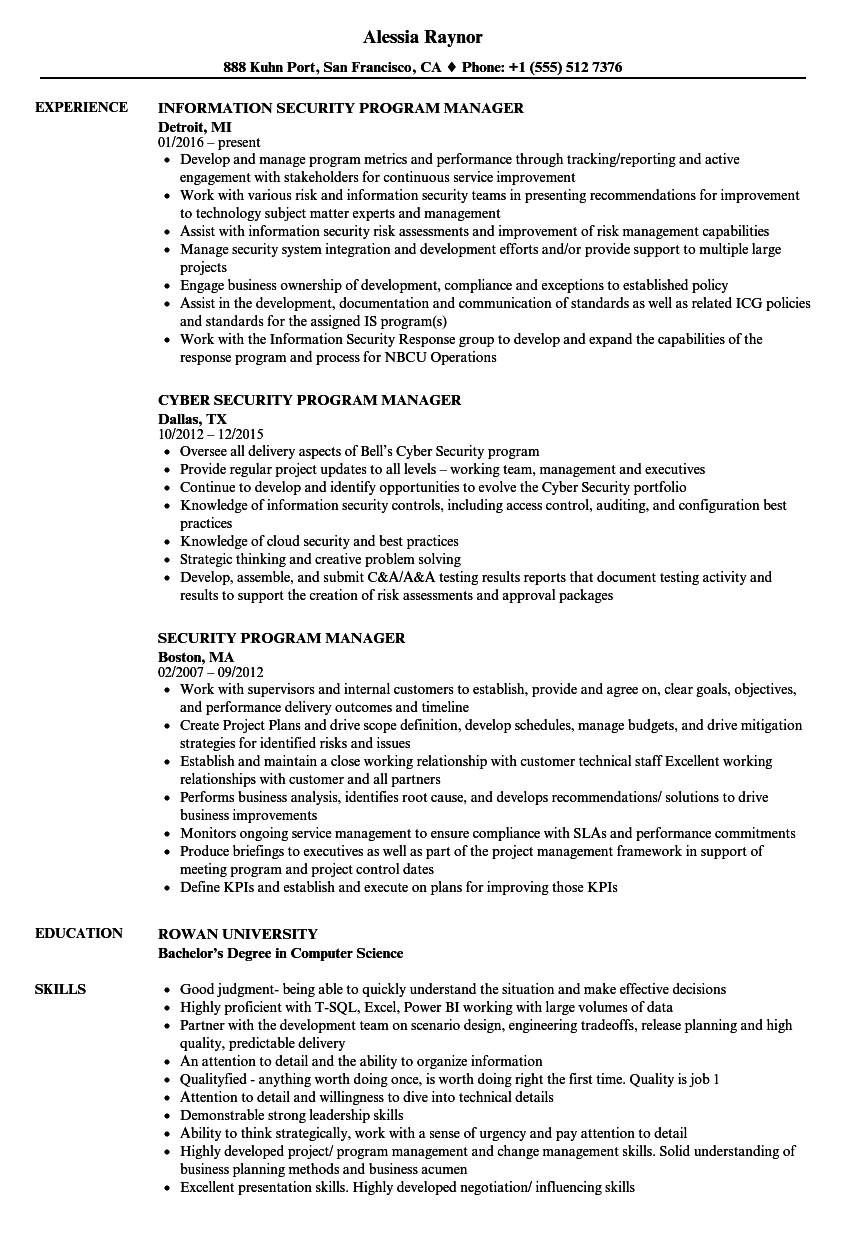
The rmf provides a disciplined structured and flexible process for managing security and privacy risk that includes information security categorization.
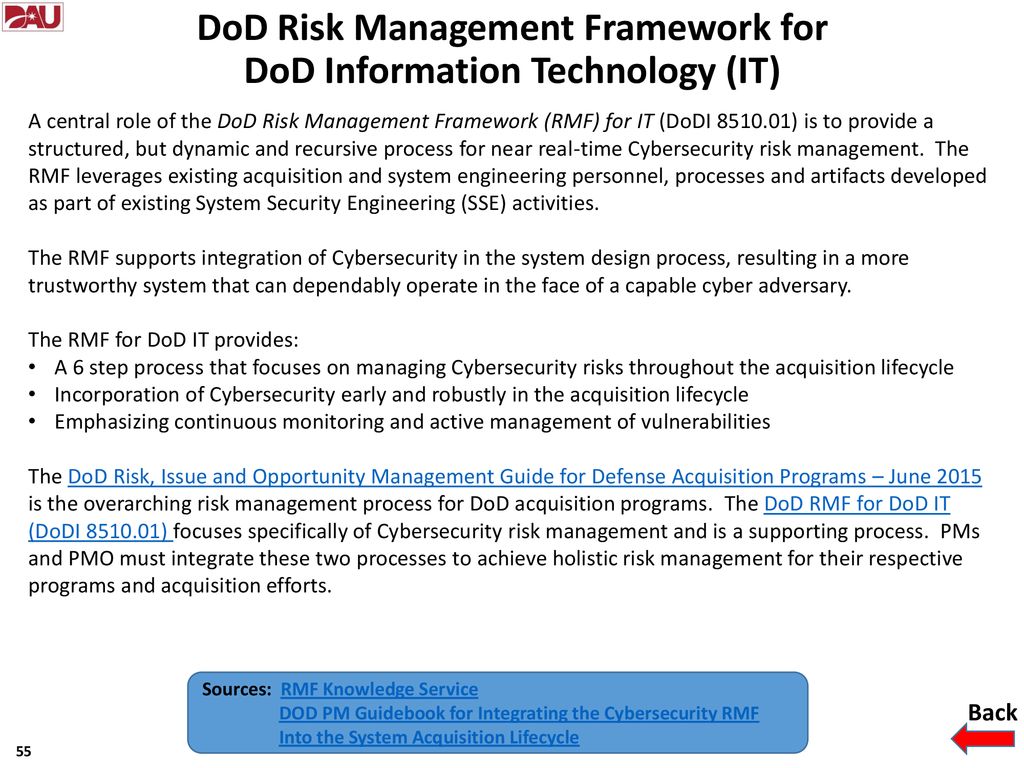
Steps of the information security program life cycle dod.
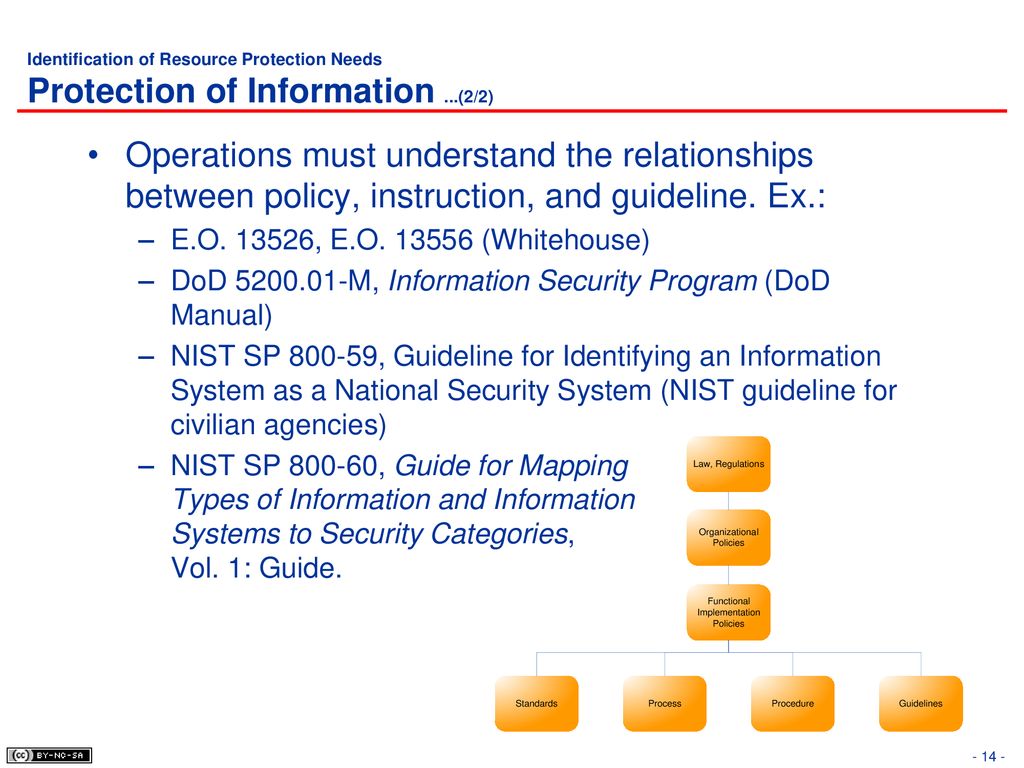
This combined guidance is known as the dod information security program.
Control selection implementation and assessment.
Dod information security program.
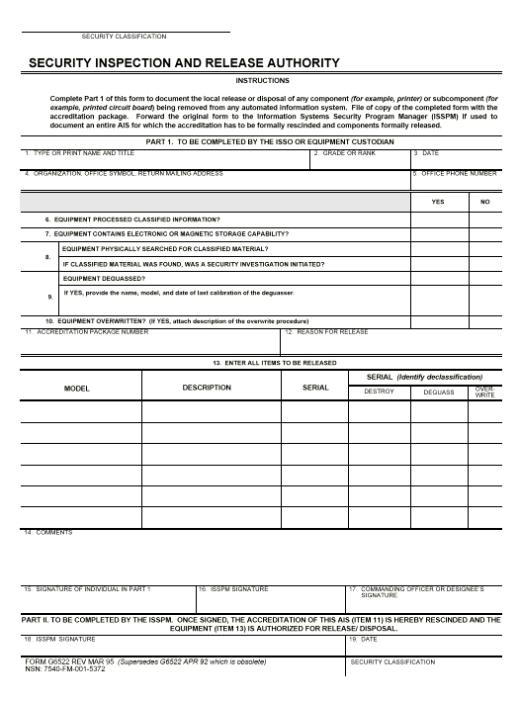
2 provides guidance for classification and declassification of dod information that requires protection in the interest of the national security.
This publication describes the risk management framework rmf and provides guidelines for applying the rmf to information systems and organizations.
The selection and specification of security controls for a system is accomplished as part of an organization wide information security program that involves the management of organizational risk that is the risk to the organization or to individuals associated with the operation of a system.
It is important to understand that a security program has a continuous life cycle that should be constantly.
A information security program is the set of controls that an organization must govern.
Classification safeguarding dissemination declassification and destruction the unauthorized disclosure of confidential information could reasonably be expected to cause to our national security.
System and common control authorizations.
It covers the information security program lifecycle which includes who what how when and.
The management of organizational risk is a key element in the organization s information security.
1 describes the dod information security program.
During this course you will learn about the dod information security program.
The six steps of the pdlc are analyse the problem design the program code the program test and debug the program formalize the solution and maintain the program.
Assigning a lower classification level to classified information because the information requires less protection in the interest of national security.